HTTP (Hypertext Transfer Protocol) is the default protocol used to transfer data between a Web server and a Web browser. When you open Internet Explorer, Chrome, Firefox or Safari and type a URL in the address bar (for example, https://www.datayard.us); you’re actually sending an HTTP request to DataYard’s Web server requesting information; in this case DataYard’s homepage. When DataYard’s Web server receives this request, it searches for the desired information and responds to your Web browser with the appropriate information. This information is then displayed on your monitor and the HTTP connection is closed. If you were to click on any link within the home page, another HTTP request is sent to the Web server and it responds with the desired data and again displayed on your monitor.
HTTP is inherently insecure, meaning information is sent in plan or clear text. Why is this noteworthy? If a savvy person were to “snoop” on your Internet connection, they’d be able to read the data rather easily using simple tools found all over the Internet. This isn’t such a bother when you’re browsing for the latest football scores or reading up on recent events. However, if you’re paying bills, checking bank accounts or attempting to secure a loan of some type via an online finance tool, this becomes seriously concerning. The answer: HTTPS.
HTTPS (Hypertext Transfer Protocol Secure), as its name implies, is HTTP’s much more secure brother. If you were to type “google.com” into your favorite browser, you’ll likely see the address change and it’ll look like this…
Why is this, though? It’s because Google uses an SSL (Secure Socket Layer) certificate to encrypt data sent between their Web servers and your Web browser. Much the same can be said about almost any other Web domain that would be expected to serve up sensitive information (banks, online shopping, investment entities, utility companies that accept online payments, etc.). Without this certificate or HTTPS, if you were to complete an online shopping transaction and someone happened to be “snooping” on your device or Internet connection, they’d be able to see the details of your purchase in plain or clear text. Credit card information, shipping addresses and other details of your transactions would be wide open for the world to see. So how does HTTPS work exactly?
When an SSL certificate is purchased and placed on a Web server, the Web server holds a private key, basically an encryption algorithm that tells its public key holders how to decrypt the information its sending back and forth. Let’s take our first example of HTTP but this time we’re going to use HTTPS.
It’s time to pay bills and instead of using snail mail, you’ve opted to go green and pay online. You enter your vendors Web address in your browser, https://www.electriccompany.com. Immediately upon this request, Electric Company’s Web server will send your browser a public key, instructions on how to decrypt the encrypted information via the private key. Confused yet? You shouldn’t be. All this decrypting and encrypting is transparent to the user and is exclusively handled by the browser and server.
As you enter your credit card information and click “SUBMIT”, your credit card information, account details and other personally identifiable information is sent to the Web server within a snug, tightly-wrapped blanket of human-unreadable characters that can only be deciphered by the Web server and it’s private key. So the guy that’s been “snooping” on your Internet connection would only see a very lengthy and incoherent string of characters that would envy Da Vinci’s cryptex.
Now that you have a better understanding of HTTP and HTTPS, as well as their differences and advantages; how does one go about “securing” their Web site? It’s rather simple, actually and as more and more people conduct sensitive business in our technologically endowed world, certificate authorities (CA) are making this process even more streamlined than before.
Companies like VeriSign, GeoTrust, DigiCert and GoDaddy specialize in the sale and deployment of SSL certificates on a global scale. A user would simply purchase an SSL certificate from any of these CA’s then install the certificate on the appropriate Web Server(s). Once the installation is complete, any browser requesting information from that Web server would then have the benefits and peace of mind that all the transactions would be safe and secure! If you’re not up for the task just let us know and we’ll be sure to take care of everything giving you a wonderful gift, peace of mind.



 On top of getting our RFID to work, we also were able to get the Pi zero USB hub to work. This wasn’t a huge issue to fix, but once we hooked it up to the Pi we were worried that we might not be able to use a port on it for serial communication. On the Pi 3 we were using before there was a dedicated serial port, COM0, which we weren’t sure the USB hub had. However it did, and we were able to continue on with using the Pi zero.
On top of getting our RFID to work, we also were able to get the Pi zero USB hub to work. This wasn’t a huge issue to fix, but once we hooked it up to the Pi we were worried that we might not be able to use a port on it for serial communication. On the Pi 3 we were using before there was a dedicated serial port, COM0, which we weren’t sure the USB hub had. However it did, and we were able to continue on with using the Pi zero. After some preliminary testing with the new inductive charging, we were able to confirm that it does charge our LiPo battery at a much quicker rate, and more efficiently, than our last set of coils. As of today we’ve also done some testing with our IR and making turns with it, and have decided on a new process that will eliminate the use of RFID tags to turn the Roomba. We will strictly use the IR for movement, and RFID for data points and positioning. Our current IR has 6 sensors; we decided to keep the black line centered between sensors 3 and 4, rather than correcting to other sensors. From there, if the Roomba reaches an intersection and sensors 1, 2 and 3 are covered, it will make a 90 degree left turn. If sensors 4, 5 and 6 are covered, it will make a 90 degree right turn. If sensors 1-6 are covered, it will make a 180 degree turn and continue on path.
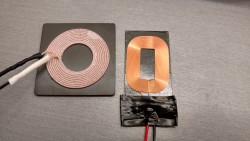
After some preliminary testing with the new inductive charging, we were able to confirm that it does charge our LiPo battery at a much quicker rate, and more efficiently, than our last set of coils. As of today we’ve also done some testing with our IR and making turns with it, and have decided on a new process that will eliminate the use of RFID tags to turn the Roomba. We will strictly use the IR for movement, and RFID for data points and positioning. Our current IR has 6 sensors; we decided to keep the black line centered between sensors 3 and 4, rather than correcting to other sensors. From there, if the Roomba reaches an intersection and sensors 1, 2 and 3 are covered, it will make a 90 degree left turn. If sensors 4, 5 and 6 are covered, it will make a 90 degree right turn. If sensors 1-6 are covered, it will make a 180 degree turn and continue on path.