
Kettering Health Cyberattack: Cyber Resilience Lessons for Every Business
The Kettering Health cyberattack is a reminder that no organization



No organization is immune to a cyberattack. Here’s what the 2025 Kettering Health ransomware attack looked like, the lessons it left behind, and what your business should do right now.
Events surrounding the Kettering Health cyberattack in 2025 reignited a critical conversation in our current threat landscape; no organization (regardless of size or industry) is immune to a serious cyber incident.
What’s already clear from how this incident unfolded: cyberattacks don’t just take down systems. They disrupt people, halt critical workflows, and erode the trust you’ve worked hard to build.
For businesses across sectors – manufacturing, professional services, healthcare, logistics – this is a direct reminder that resilience isn’t optional anymore. It’s a core business requirement. Let’s first start with what happened during the Kettering Health Cyberattack.
Disclaimer: This article is based on publicly available information and is provided for general informational and educational purposes only. Details surrounding cybersecurity incidents may change as new information becomes available. This content does not constitute a full investigation or technical assessment of any specific organization and should not be interpreted as definitive statements about any entity’s systems, actions, or response.
On May 20, 2025, Kettering Health – a nonprofit healthcare network operating 14 medical centers and more than 120 outpatient facilities across western Ohio, employing over 15,000 people – experienced a ransomware attack that caused a system-wide technology outage (BleepingComputer).
The attack was carried out by the Interlock ransomware group, which encrypted critical systems including phone lines, the MyChart patient portal, and core patient care applications (BleepingComputer). The group claimed to have stolen over 941 GB of data and threatened to publish it on the dark web if Kettering did not respond within 72 hours (HIPAA Journal, Dayton Daily News).
Kettering Health responded immediately – choosing not to pay the ransom – and shut down approximately 600 digital applications to contain the threat (HIPAA Journal). As the organization worked to secure and restore its systems, elective procedures were canceled, emergency departments temporarily diverted ambulances, and clinical staff shifted to manual, pen-and-paper workflows (Dayton Daily News, TechCrunch). As Kettering Health stated in their incident report: “We responded immediately to secure our systems and protect patient data. Since then, we have been restoring systems and enhancing security” (Kettering Health).
Full recovery took time – as the CEO noted, healthcare outages of this nature typically last 10 to 20 days (WCPO). Kettering Health returned to normal operations on June 10, 2025 (HIPAA Journal).
To see Kettering Health’s full outage breakdown with dates and times, see Kettering Health System-Wide Outage.
Kettering Health is far from alone in facing this type of threat. It joins a growing list of healthcare organizations targeted by ransomware in recent years, including Change Healthcare, Ascension Health, and DaVita (TechCrunch).
Understanding what unfolds during an incident is the first step toward preparing for one. Organizations typically face a rapid combination of challenges:
Even well-managed IT environments aren’t immune. The difference between a minor incident and a major crisis often comes down to how quickly your team can detect the attack, contain it, and recover from it.
Rather than dissecting any single organization’s response, here are the broader lessons that apply to virtually every business.
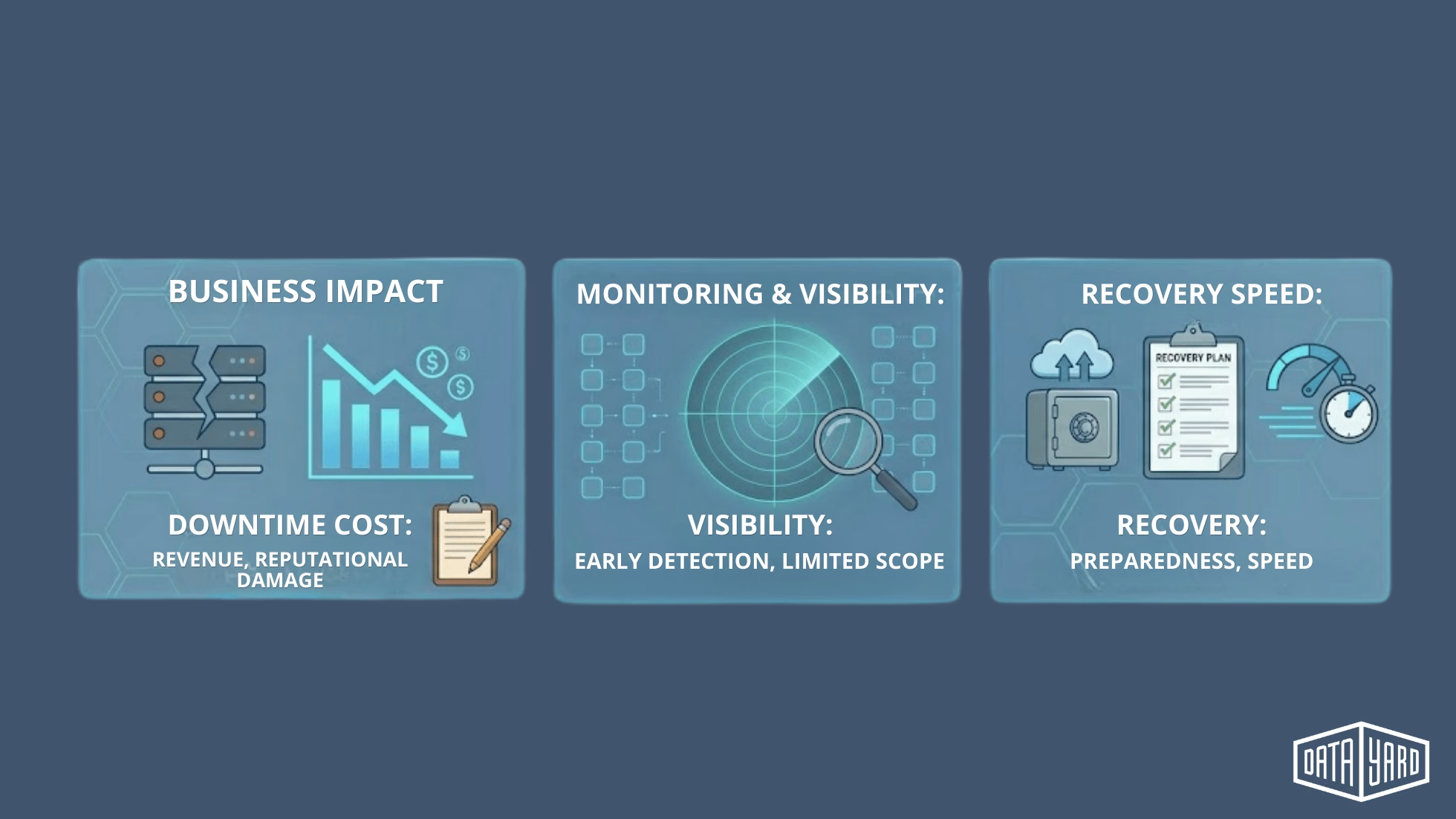
When systems go down (even briefly), teams scramble to manual processes or halt work entirely. Customer-facing operations stall. Revenue slows. Reputational damage accumulates by the hour. The financial cost of unplanned downtime is often far higher than the cost of the preventive measures that could have avoided it.
Many cyberattacks go undetected for days or weeks. Early detection is one of the highest-leverage investments an organization can make. The faster you spot an anomaly, the smaller the blast radius.
There’s no such thing as a 100% secure environment. The organizations that fare best aren’t just the ones that block the attack — they’re the ones that have a plan for what to do if something gets through.
Prevention is about reducing your attack surface and making it harder for threats to succeed — not achieving an impossible standard of perfect security. Cyberattacks are constantly evolving, and no environment is completely immune. The following suggestions help create meaningful friction for attackers and significantly reduce your risk of a successful breach.

A strong baseline to cyberattack prevention includes:
Least-privilege access policies so compromised credentials do limited damage.
Regular OS and application updates.
Vulnerability scanning with structured remediation workflows.
Regular end user cybersecurity awareness training
These controls create meaningful friction for attackers, but they must be paired with something equally important: a tested recovery plan.
Not sure how your current environment stacks up or where security gaps might exist?
We can help you evaluate your current setup, identify areas of risk, and prioritize the changes that will have the biggest impact on your security and resilience.
When an incident occurs, the first few minutes matter enormously.
Here’s a response framework that works.
Isolate affected systems from the rest of your network.
Disable or rotate compromised credentials immediately.
Block lateral movement before it spreads further.
Engage your internal team and any external security partners.
Document every action taken — this is critical for post-incident analysis and potential legal requirements.
Maintain clear, factual communication with leadership and key stakeholders.
Activate backup systems or failover environments.
Prioritize your most critical applications and workflows.
Restore only from clean, verified backups.
Validate full system integrity before bringing anything back online.
This is where organizations are either prepared or left with real gaps in their resilience. A modern disaster recovery strategy isn’t just about having backups. It’s about having the right backups, regularly tested, in an architecture that’s designed to recover fast.

A modern disaster recovery strategy should include:
Immutable backups cannot be altered or encrypted by ransomware — a critical distinction.
Regular recovery testing (not just backup success logs).
Two metrics every organization should know:
If you don’t have documented answers to both of those questions, your disaster recovery plan isn’t complete.
In practice, the difference between a well-designed, regularly tested recovery strategy and an untested one often comes down to whether your business is down for hours or for days.
At DataYard, we’ve seen firsthand how much infrastructure design can impact real-world outcomes. Supporting high-demand platforms like MegaMillions during their billion-dollar lottery events requires environments built for extreme availability — where performance, redundancy, and rapid recovery are all taken into account.
That same philosophy applies directly to cybersecurity resilience. Environments designed with recovery in mind can significantly reduce downtime — from days to hours — depending on how systems are architected and tested.
The most important takeaway from events like the Kettering Health cyberattack isn’t fear — it’s urgency around preparation.
Organizations that invest in proactive monitoring, well-architected infrastructure, tested disaster recovery, and experienced engineers are in a measurably stronger position to maintain operations when incidents occur. And they do occur.
The goal isn’t just prevention. It’s the ability to recover quickly, maintain operations, and move forward with confidence.
Cyberattacks are no longer rare events; they’re an operational reality. If you’re not confident in how your environment would perform during a cyber incident or how long recovery would actually take, it’s worth addressing now, before it becomes urgent.
We can walk through your current setup, identify gaps in security, uptime, and recovery planning, and give you a clear picture of where you stand.
BleepingComputer. Kettering Health Hit by System-Wide Outage After Ransomware Attack.
TechCrunch. Health Giant Kettering Still Facing Disruption Weeks After Ransomware Attack.
Dayton Daily News. Cyberattack Brings Down Kettering Health Phone Lines, MyChart Patient Portal Access.
WCPO. Kettering Health CEO Provides an Update After Cybersecurity Incident Results in Outage.
HIPAA Journal. Kettering Health Ransomware Attack — Incident Summary and Analysis.
Kettering Health. System-wide Technology Outage.
Kettering Health. Cybersecurity Incident – Frequently Asked Questions.

The Kettering Health cyberattack is a reminder that no organization
A DDoS (Distributed Denial of Service) attack floods your infrastructure

What’s the best cloud hosting for scaling websites during traffic