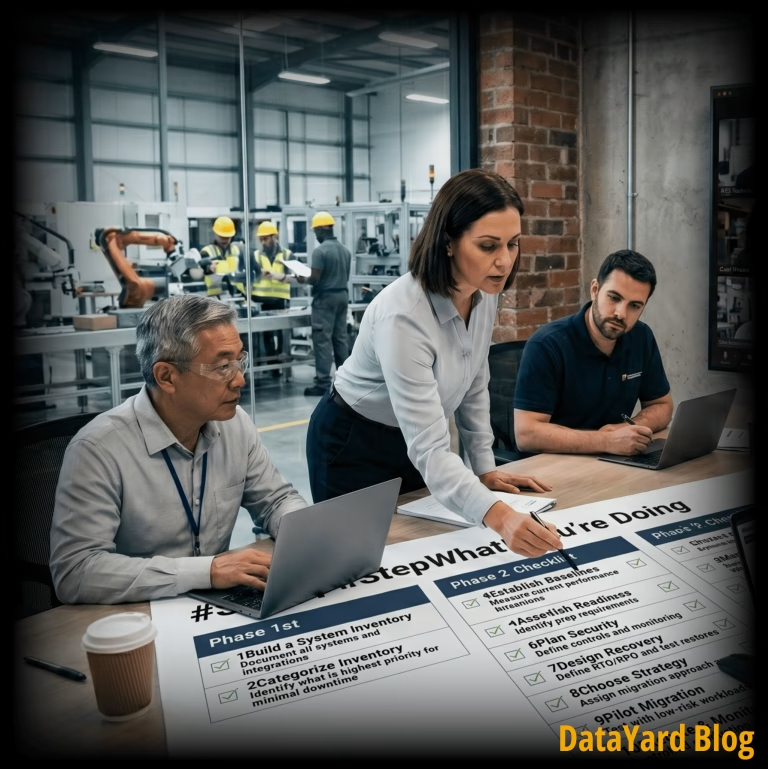
Cloud Migration Checklist for Manufacturing Companies
Manufacturing cloud migrations require careful planning to avoid extended downtime
In this blog, we will cover how to stop a DDoS attack, what causes these attacks, and 6 common mitigation strategies, followed by answers to frequently asked questions.
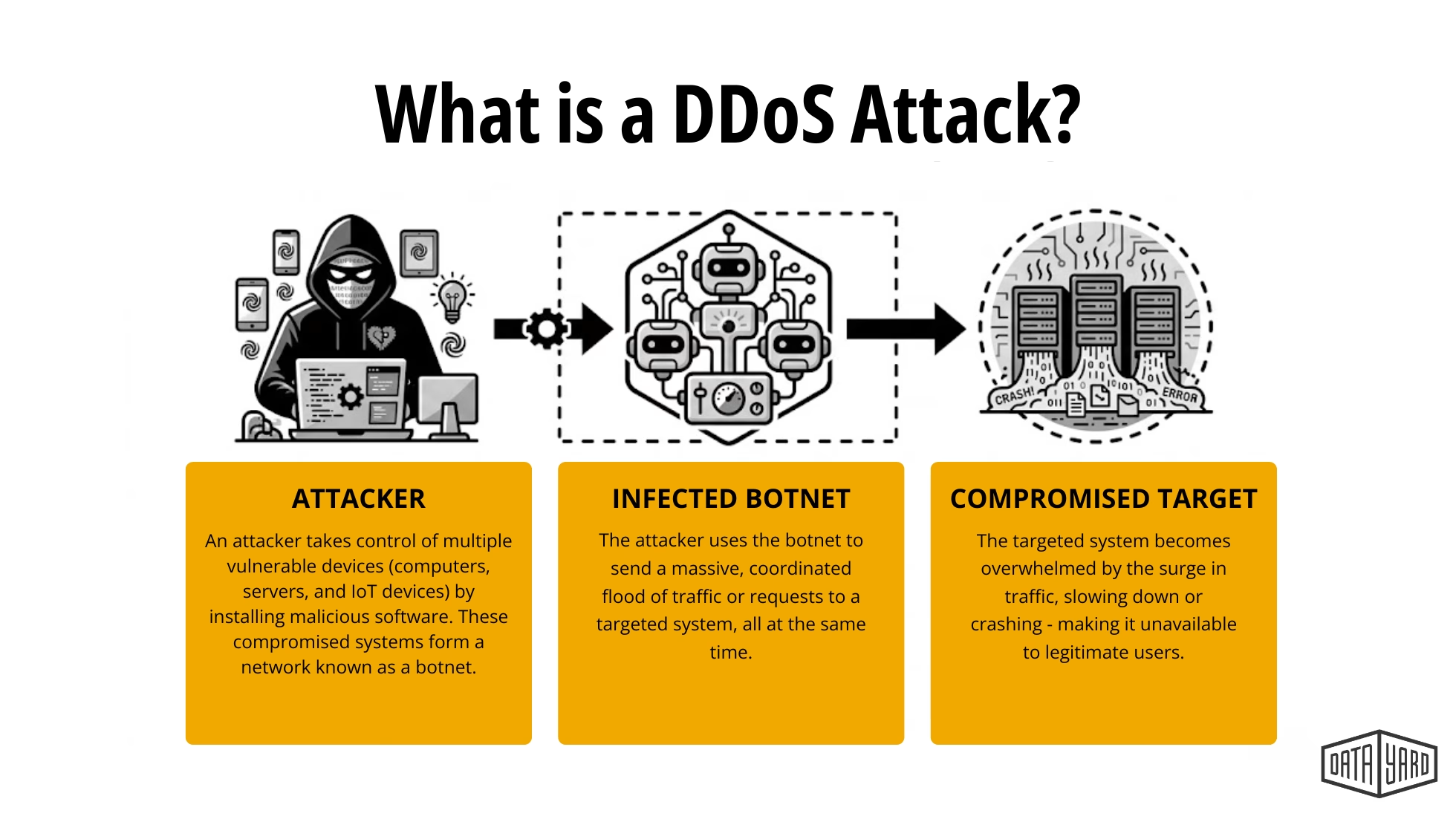
A DDoS (Distributed Denial of Service) attack floods hosting infrastructure with traffic from thousands of sources within a short period of time, making a website or application unavailable to legitimate users.
Motivations behind DDoS attacks vary. Security researchers note that some attackers launch these attacks to exploit vulnerabilities or disrupt services, while others attempt to extort organizations or cause downtime that damages revenue and customer trust (Fortinet).
Stopping or mitigating a DDoS attack typically requires a layered defense strategy. No single tool can completely prevent these attacks, but combining multiple protections — such as CDN filtering, scalable cloud infrastructure, hardened security configurations, and continuous monitoring — can significantly reduce risk.
Below are 6 commonly used strategies organizations rely on to stop or mitigate DDoS attacks, starting with one of the most widely deployed defenses.
DDoS attacks are designed to overwhelm infrastructure by generating artificial traffic spikes that exceed normal operating capacity.
Instead of attempting to breach a system directly, attackers attempt to exhaust resources such as:
Once those limits are reached, hosting resources can become unavailable and legitimate users can no longer access the system. Modern attacks can generate substantial volumes of traffic, sometimes exceeding the capacity of traditional hosting environments.
DDoS attacks are also increasing in frequency and scale. Industry reports indicate that millions of attacks occur globally each year, with many targeting small and mid-sized organizations whose infrastructure may not be designed for sudden traffic floods.
The numbers from the Cloudflare 2024 Q4 Report reflect just how widespread the threat has become. The report showed the total number of DDoS attacks reached 47.1 million, representing a 236% increase compared to the previous year (Cloudflare 2025 Q4 DDoS Threat Report).
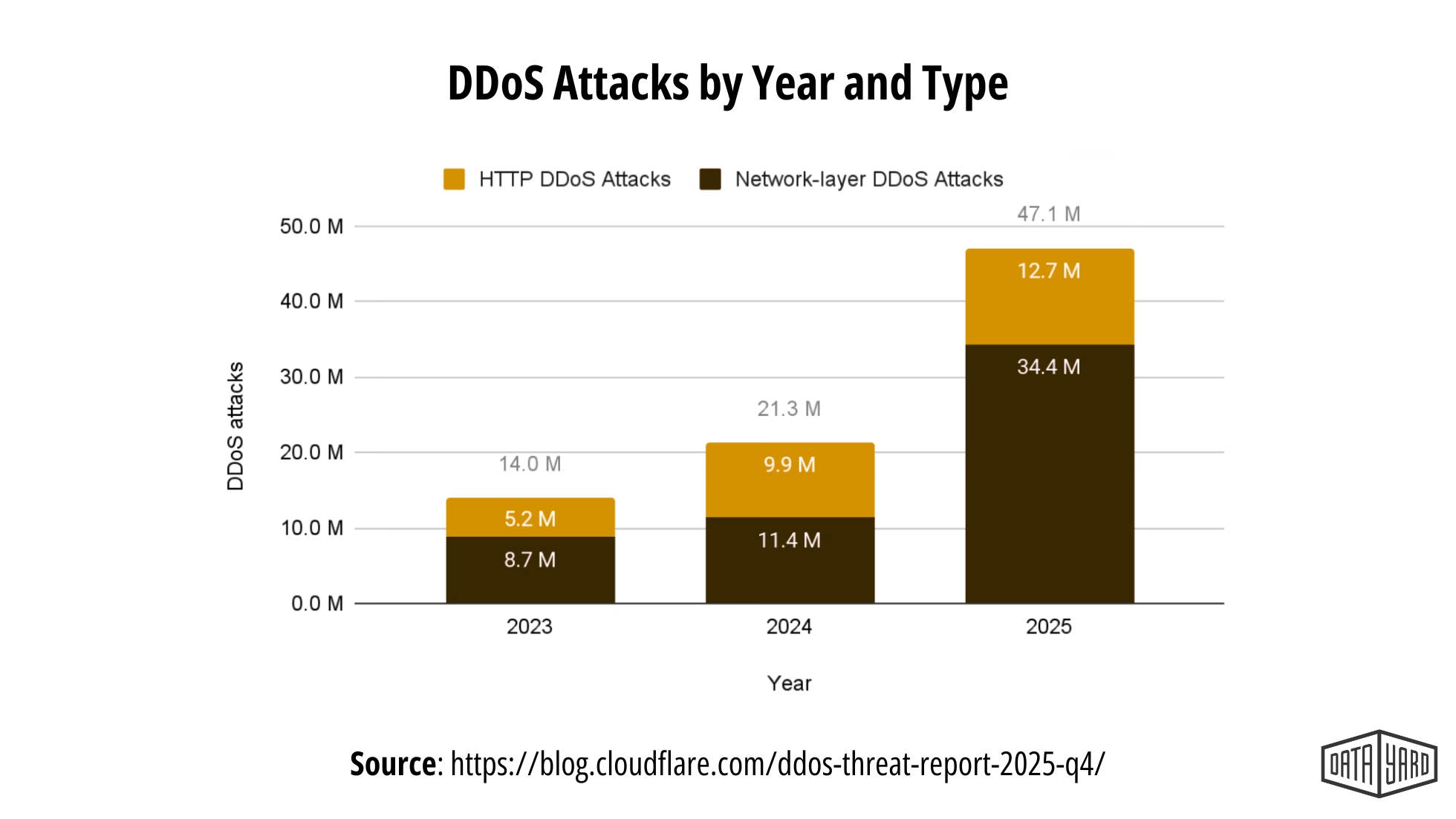
Because of this increase in attack volume, organizations increasingly rely on secure, cloud-based infrastructure, edge filtering, and proactive monitoring to maintain availability during traffic floods.
One of the most effective ways to stop a DDoS attack is by placing infrastructure behind a Content Delivery Network (CDN).
A CDN distributes traffic across a global network of servers and acts as a buffer between users and your origin infrastructure.
Benefits include:
Edge security platforms can filter, rate-limit, or absorb large volumes of traffic before it reaches your cloud infrastructure.
While a CDN handles traffic at the edge, your hosting environment also plays a critical role in surviving an attack.
Public-facing systems are frequent targets during DDoS attacks. These systems are designed to accept connections from the internet, which makes them the most visible and accessible entry points for attackers.
Common public-facing systems include:
During a DDoS attack, these systems may experience a sudden flood of traffic that can overwhelm infrastructure resources. This can lead to slow response times, degraded performance, or service interruptions for legitimate users
Hosting public-facing systems in scalable cloud environments can improve resilience during these events.
In many environments, organizations use hybrid cloud architecture, which combines private cloud infrastructure with public cloud capacity. This allows infrastructure to expand when traffic spikes occur.
This architecture can help organizations:
Scalable infrastructure does not eliminate DDoS attacks, but it can significantly improve an environment’s ability to remain available during large traffic floods.
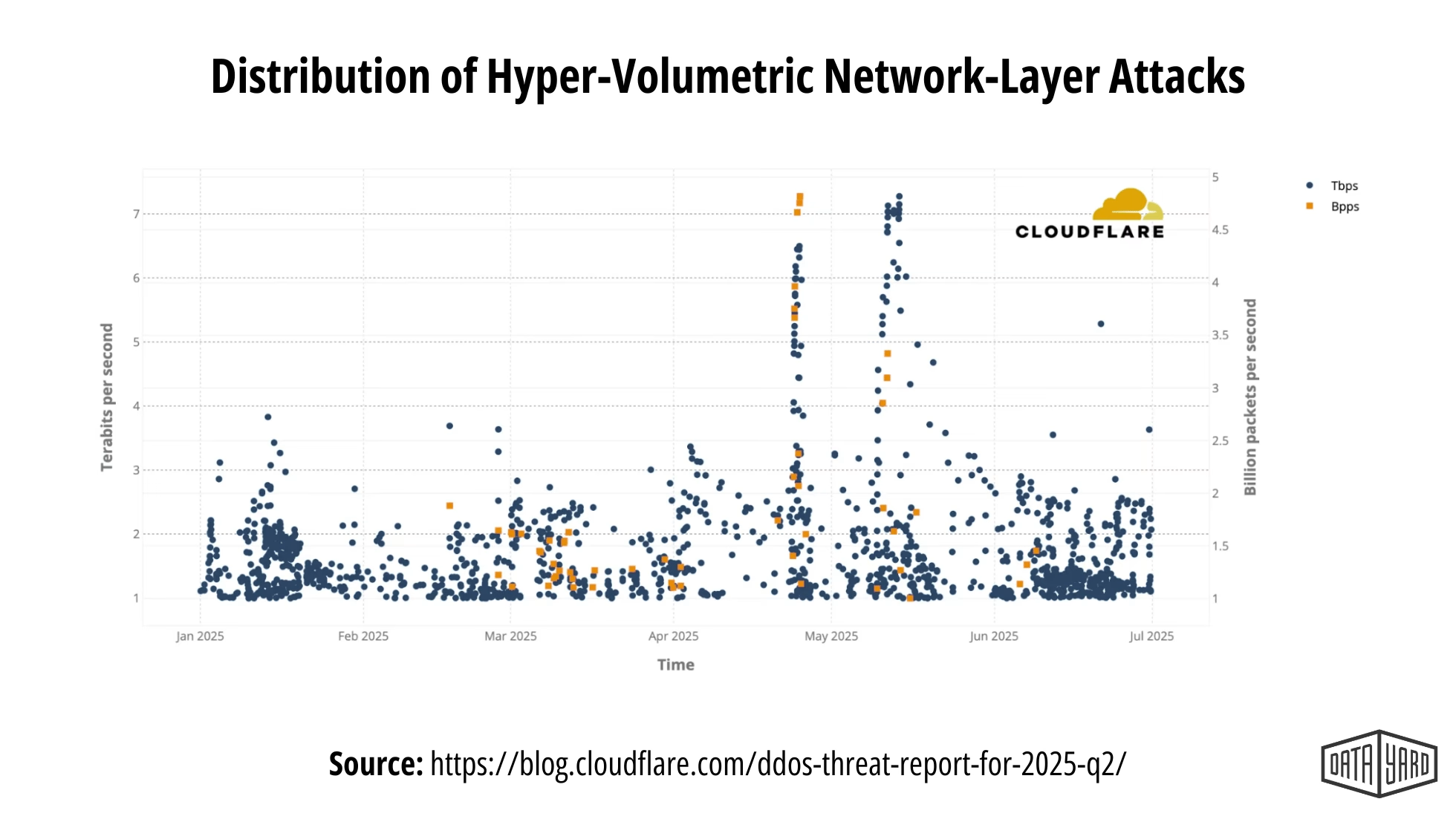
These types of events are often referred to as hyper-volumetric DDoS attacks. In the Cloudflare Q2 2025 Threat Report, some attacks exceeded one million requests per second, large enough to overwhelm many traditional hosting environments.
Organizations evaluating their infrastructure often discover that improving resilience requires both scalable architecture and ongoing operational oversight.
If you’re exploring scalable cloud infrastructure — or want to understand how your current environment would handle a large traffic event — DataYard’s engineering team can help review your architecture and recommend practical next steps.
Contact our team to start the conversation
Even with cloud infrastructure in place, your network’s first line of defense still depends heavily on how your firewalls are configured.
Firewalls play an important role in detecting and stopping certain types of DDoS attacks.
For example, SYN flood attacks exploit the TCP connection handshake by sending connection requests without completing them.
Proper firewall configuration can help mitigate these attacks by:
While firewalls alone cannot stop every DDoS attack, they remain an important layer in a broader defense strategy.
Firewall configuration can vary significantly depending on your infrastructure, traffic patterns, and security requirements. Organizations often benefit from having experienced engineers review firewall rules and network architecture to ensure protections are properly configured.
Beyond how traffic is filtered, the underlying configuration of your web servers also affects how well they hold up under pressure.
Web servers can be configured to handle abnormal traffic patterns more effectively.
Common hardening practices include:
These adjustments reduce the likelihood that attackers can exhaust server resources during high-volume traffic events.
Hardening individual servers is an important step, but protecting infrastructure as a whole also requires thoughtful network architecture.
Another strategy for mitigating DDoS attacks is isolating critical applications from public-facing services.
For example, organizations often place internal systems such as:
…on separate networks or subnets.
If public infrastructure experiences a traffic flood, these internal systems remain protected.
A well-configured cloud architecture makes this separation easier by allowing organizations to segment workloads across private and public environments.
Even with strong separation in place, attacks can still catch teams off guard without the right visibility into what’s happening across the environment.
Early detection can significantly reduce the impact of a DDoS attack.
Organizations should monitor for signs such as:
Sudden spikes in traffic
Unusual request patterns
Abnormal CPU or bandwidth usage
Unexplained performance slowdowns
Continuous monitoring tools — combined with experienced engineers reviewing system behavior — help identify abnormal traffic patterns before they escalate into outages.
Knowing the warning signs is valuable, but organizations also need a clear plan for what to do once an attack is already underway.
In a quick summary, these are the 6 strategies to stop or mitigate DDoS attacks:
Prefer a quick walkthrough? Watch our video overview below: How to Stop a DDoS Attack: 6 Strategies That Work.
Even well-protected systems may occasionally experience attack attempts.
When this happens, the focus shifts to mitigation and recovery.
Typical response steps include:
1. Analyze incoming traffic
Identify suspicious traffic patterns or abnormal request behavior.
2. Apply filtering rules
Block malicious traffic through firewalls or edge protection platforms.
3. Scale infrastructure
Increase infrastructure capacity temporarily to absorb traffic spikes.
4. Monitor system stability
Continue monitoring systems until traffic patterns return to normal.
After the incident, teams should review system logs and performance metrics to strengthen defenses for future events.
Responding effectively in the moment is critical, but the infrastructure underneath your response plan determines how much damage an attack can actually do.
Many successful attacks occur because infrastructure has fixed capacity limits. When those limits are exceeded, the system becomes unavailable.

Scalable infrastructure reduces this risk by allowing environments to expand temporarily during traffic surges — making it one of the most practical long-term strategies for mitigating DDoS attacks.
Scalable cloud architectures can:
While scalability alone does not eliminate attacks, it improves resilience during large traffic events. That resilience is further strengthened when experienced engineers are actively overseeing the environment.
If you’re exploring scalable infrastructure or managed cloud support, DataYard engineers can help evaluate your environment and recommend practical next steps.
Stopping a DDoS attack is rarely about deploying a single tool. Each of the 6 strategies above works best as part of a coordinated defense — not in isolation.
Effective protection usually combines:
Organizations operating managed cloud environments benefit from continuous oversight by engineers who can detect unusual traffic patterns and respond quickly when conditions change.
This combination of architecture, automation, and engineering oversight helps critical applications remain available during unexpected traffic events.
Have questions about implementing these 6 strategies for your organization?
DDoS attacks are designed to overwhelm infrastructure.
Protecting against them requires more than a single security tool.
Organizations that combine scalable cloud infrastructure, edge traffic filtering, hardened system configurations, and continuous monitoring are far better equipped to maintain uptime during traffic floods.
DataYard helps organizations design and manage resilient cloud environments built for reliability, scalability, and continuous operational oversight.
If your website or application is critical to your business operations, preparing before an attack occurs is the most effective way to keep critical systems online.
Talk with our team about strengthening your infrastructure.
Manufacturing cloud migrations require careful planning to avoid extended downtime
Many manufacturers rely on legacy systems that still power critical

The Kettering Health cyberattack is a reminder that no organization